If you attend any security conference, you will inevitably hear pentesters boasting that they can break into any company by dropping malicious USB drives in the companys parking lot. This anecdote is so famous that it was the featured in the TV show Mister Robot in episode 6. This left us wondering---does this attack actually work or is it merely a myth?
To put this attack to the test, we dropped nearly 300 USB sticks on the University of Illinois Urbana-Champaign campus and measured who plugged in the drives. We find that users picked up, plugged in, and clicked on files in 48% of the drives we dropped. They did so quickly: the first drive was connected in under six minutes. This blog post summarizes how we ran the study, highlights the key findings, looks at what motivates people to plug in USB sticks, and discusses possible mitigations to improve USB security.
This large scale study, paper available here, was done with the help of my co-conspirators of the University of Illinois and the University of Michigan and was published in May 2016 at the 37th IEEE Security and Privacy Symposium. I also presented these results as part in my Blackhat talk about USB keys:
Experimental setup
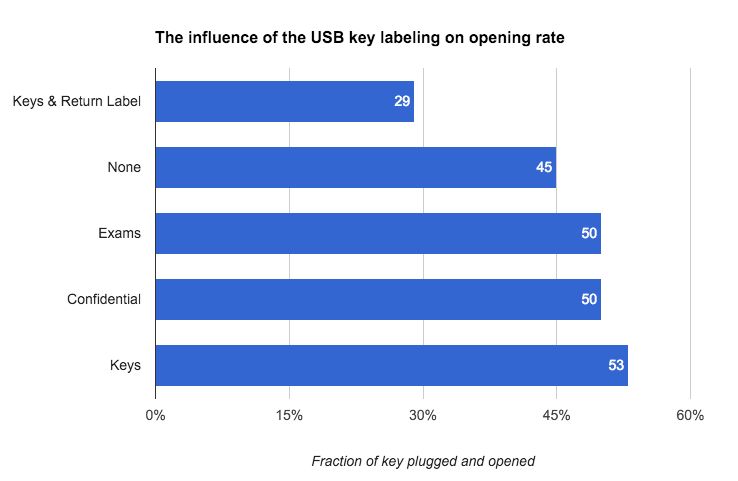
To test whether users pick up drives they find on the ground, we dropped five types of drives on the University of Illinois campus: drives labeled exams or confidential, drives with attached keys, drives with keys return address label, and generic unlabeled drives.

On each drive, we added files consistent with the drives label: private files for the sticks with no label, keys or a return label; business files for the confidential one; and exam files for the exam drives. We show an example screenshot of a drive containing personal files below. All the files were actually HTML files with an embedded image on our server. This allowed us to detect when a drive was connected and a file opened without executing any unexpected code on the users computer. When a user opened the HTML file, we asked them if they wanted to opt out or to answer a survey about why they plugged in the drive in exchange of a gift card. 62 users (~20%) agreed to respond.

Dropping malicious USB sticks is very effective
So how effective is it to drop malicious USB keys to compromise computers? Turns out it is very effective: 48% of the drives we dropped were not only plugged but also had at least one file opened. This surprisingly high conversion rate demonstrate that USB drop attacks are a real threat and underscores the importance of educating users on the risk of plugging in untrusted USB devices. This result indicates that while weaponizing a mouseis a cool idea, it is not needed in practice to trick users.
Dropping malicious USB keys gives results very quickly
Not only do many people plug in USB devices, they connect them quickly. 20% of the connected drives were connected within the first hour and 50% were connected within 7 hours as visible in the graph below.
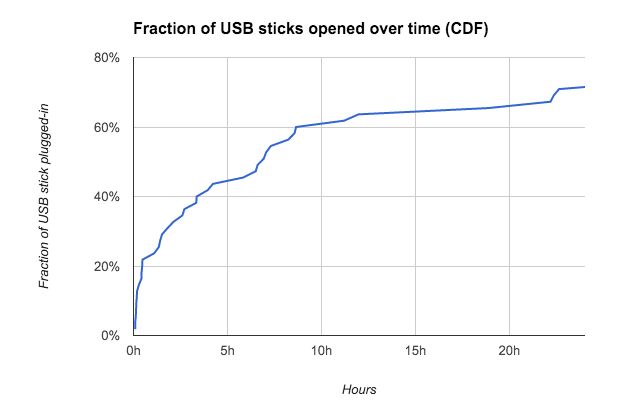
This means that the windows of time available to detect that this attack is occurring is very short. In our case our experiment the first report of the presence of weird USB keys on the campus only started to surface on Redditroughly 24 hours after the first wave but this didnt prevent people to keep plug-in our USB sticks.
The appearance of usb key (somewhat) matters
As visible on the chart below, USB sticks with labels that invoke curiosity are more likely to be opened than USB sticks without any distinctive marking. The surprising part is that attaching physical keys to elicit altruistic behavior was most effective. As discussed below, altruistic behavior is the number one reason users report for opening the keys. Keys with an attached return label were the least open likely because people had another mean to find the owner. Note that the differences in opening rate are NOT statistically significant, except that the drives with return labels were less frequently connected.
Malicious USB stick drop location does not matter
As visible in the chart above, the opening rate for every location was roughly the same. This confirms that the attacker dont have to break into the facility to carry out this attack effectively. Dropping the drive in a parking lot is as effective as leaving it in a protected conference room.

Everyone is vulnerable to USB drop attacks
Everyone is vulnerable to USB drop attacks: we found no difference between the demography, security knowledge and education of the users who plugged USB drives and the general population of the UIUC university according to our survey. Why being more security savvy is not negatively correlated with being less vulnerable is everyone guess. It raise the question of the effectiveness of security education at preventing breaches. A subject that seems worth investigating significantly more to ensure that security training really helps people to be safer.
Users Motivation
Self reported motivation: When asked why did they plugged the drive most survey respondents claimed it was for the altruistic purpose of returning the drive to its owner (68%). Only 18% said they were motivated by curiosity as visible in the pie chart below.
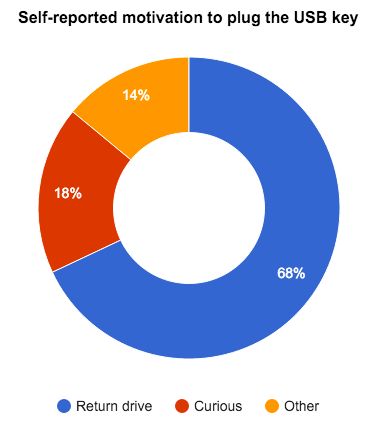
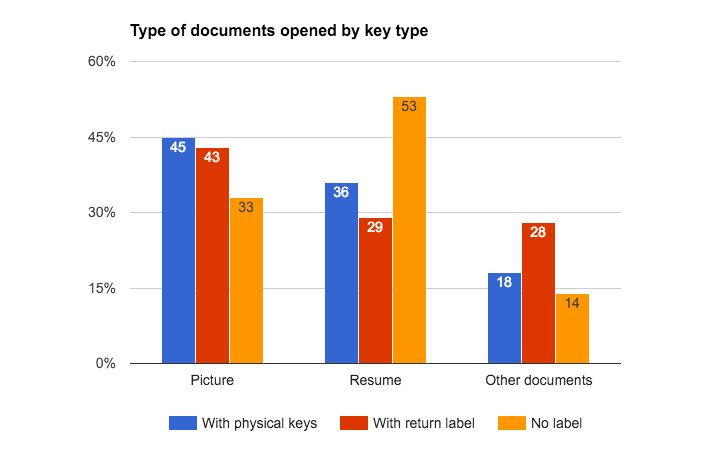
Observed motivation: However as visible in the chart below the self reported motivation is not consistent with which files were accessed. For example for the drives with physical keys attached, users clicked on winter break pictures more often than on the resume file, which would have contact information of the owner. Interestingly the same behavior is observed for the drives with a return label, but not for the drives with no marking.
Improving USB security
This study show cases that USB security is a real concern and dropping USB drives is a cheap and practical attack vector. Here are three potential strategies to do improve your USB security posture:
-
Educate users: Take the time to inform your relatives, friends, and co-workers about the danger of untrusted USB devices. As a first quick step, how about sharing this post with them? Longer term we need to make sure rogue USB devices are covered in security training. To make this easier, I will make our slides available when they are ready. To get notified when this happen you can subscribe to my blog mailing list or follow me on your favorite social network (link below).
-
Ban USB drives: You can enforce a policy to forbid the use of USB drives. On Windows this can be done by denying users access to the Usbstor.inf file. With the advent of cloud storage and fast internet connections, this is policy is not as unreasonable as it was a few years back.
-
**Prevent untrusted USB devices from being connected:**To do so you can use killusb, a tool developed to thwart FBI computer seizure, to instantly reboot computers when an unknown USB devices is connected. This can cause issues when you allow people to plug their own mouse, but I think kill USB can be hacked to only target specific devices class. If you ever come around doing this let me know and I will update this post.
Let me know how you are protecting yourself against USB attacks on your favorite social network.




